
How To: Sniff the WhatsApp password from your Android phone or iPhone
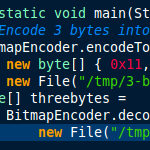
WhatsApp is a very popular SMS-like messenger for smartphones, but it’s unfortunately only available for smartphones right now. If you want to use other tools or write web applications that send or receive WhatsApp messages (e.g. WhatsAPI, was at https://github.com/venomous0x/WhatsAPI, site now defunct, July 2019), you have to find a way to sniff the WhatsApp password from your smartphone. Until recently, this password was just an MD5 hash of your IMEI (or MAC address), but that has changed when that was uncovered. Since then, the WhatsApp server assigns a password to each device/account when it first registers.
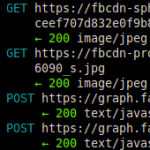
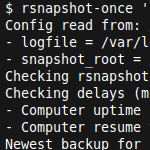
This tutorial demonstrates how to capture the WhatsApp password of your WhatsApp account using the SSL/TLS proxy mitmproxy. Once you have this password, you can use it to communicate with the WhatsApp servers directly or via a framework. This is the first part of a two-part tutorial. The second part demonstrates how to send and receive WhatsApp messages via PHP.






Recent Comments